PROJECTS IN CRYPTOGRAPHY
Projects in Cryptography are developed for providing security in much kind of applications like military, crime detection and cloud process. Generally, cryptography is the secret written of art for some critical situation. Important service behind in the cryptography should thwart transmission of data between persons. In a cryptography system transmission can be occurred with the help of network communication paths. According to that medium we have to store the sensitive information in a secured manner.
Projects in Cryptography should be closely related to steganography and to provide the security. This cryptography system must depend on the algorithms called as cryptographic algorithms. This cryptographic algorithm can be divided into symmetric key cryptographic algorithms and asymmetric key cryptographic algorithms. It can also be depends on the concept of secret value also known as key. For processing difficult algorithms we have to add some additional key values. With the help of those keys new kind of algorithms should exploits reversible scuttle of information. Very secret communication may be done with the help of creating new algorithms with high level of security.
Normally, when a cryptosystem technique has two kinds of ciphering algorithms names are enciphering algorithm and deciphering algorithm. Crypt Analysis process should restrict the ciphertext information from the intruders or enemies in the network. The types of cryptography are mainly classified into public. Secret and hash function. Mostly, the projects in cryptography may be created based on types of cryptography. In a public key cryptography both the process of encryption and decryption uses different keys. In public key cryptography algorithm encryption keys are to be made publicly. Here, the sender can encrypt the file with public key but the receiver can extract the plain text from that using separate private key.
Strength of encryption process can be gathered from the process of length of key, secrecy of key, initialization vectors and the working process together. Sensitive information’s are focused to provide more security with the help of any factors in the cryptography like non-repudiation, integrity, authentication and confidentiality. Mostly, the projects in cryptography should be developed using the public-key cryptography.
Public or asymmetric cryptography, need to help the transmission process between encryption and decryption. But this public key cryptography the keys are represented in asymmetric manner. The asymmetric key cryptography algorithm should have both private key and public key. This public based cryptography projects will accessible for all users. These kind of security based projects are developed under the domain of information forensics and security.
Subscribe Our Youtube Channel
You can Watch all Subjects Matlab & Simulink latest Innovative Project Results
Our services
We want to support Uncompromise Matlab service for all your Requirements Our Reseachers and Technical team keep update the technology for all subjects ,We assure We Meet out Your Needs.
Our Services
- Matlab Research Paper Help
- Matlab assignment help
- Matlab Project Help
- Matlab Homework Help
- Simulink assignment help
- Simulink Project Help
- Simulink Homework Help
- Matlab Research Paper Help
- NS3 Research Paper Help
- Omnet++ Research Paper Help
Our Benefits
- Customised Matlab Assignments
- Global Assignment Knowledge
- Best Assignment Writers
- Certified Matlab Trainers
- Experienced Matlab Developers
- Over 400k+ Satisfied Students
- Ontime support
- Best Price Guarantee
- Plagiarism Free Work
- Correct Citations
Expert Matlab services just 1-click

Delivery Materials
Unlimited support we offer you
For better understanding purpose we provide following Materials for all Kind of Research & Assignment & Homework service.
 Programs
Programs Designs
Designs Simulations
Simulations Results
Results Graphs
Graphs Result snapshot
Result snapshot Video Tutorial
Video Tutorial Instructions Profile
Instructions Profile  Sofware Install Guide
Sofware Install Guide Execution Guidance
Execution Guidance  Explanations
Explanations Implement Plan
Implement Plan
Matlab Projects
Matlab projects innovators has laid our steps in all dimension related to math works.Our concern support matlab projects for more than 10 years.Many Research scholars are benefited by our matlab projects service.We are trusted institution who supplies matlab projects for many universities and colleges.
Reasons to choose Matlab Projects .org???
Our Service are widely utilized by Research centers.More than 5000+ Projects & Thesis has been provided by us to Students & Research Scholars. All current mathworks software versions are being updated by us.
Our concern has provided the required solution for all the above mention technical problems required by clients with best Customer Support.
- Novel Idea
- Ontime Delivery
- Best Prices
- Unique Work
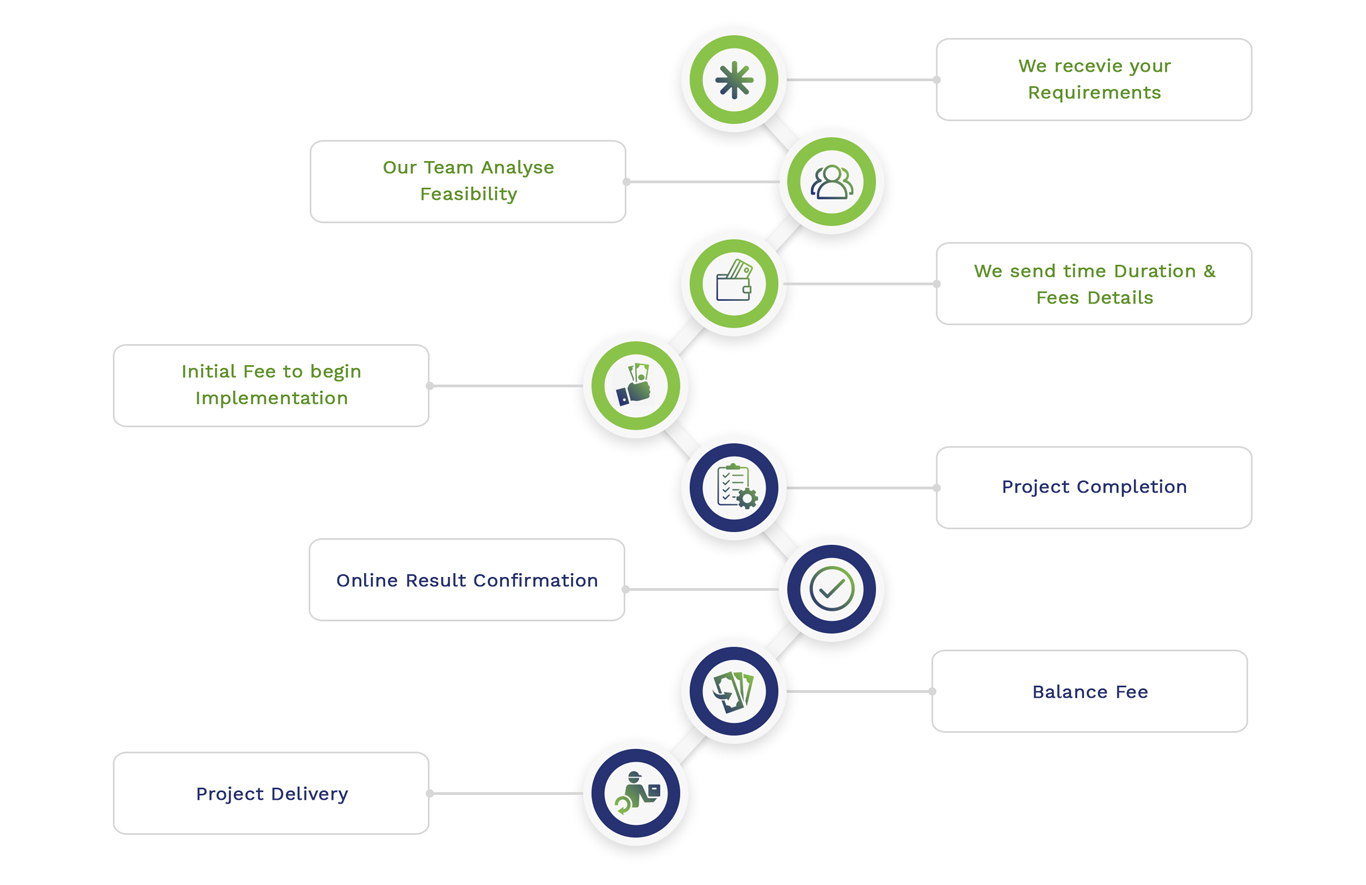
Simulation Projects Workflow
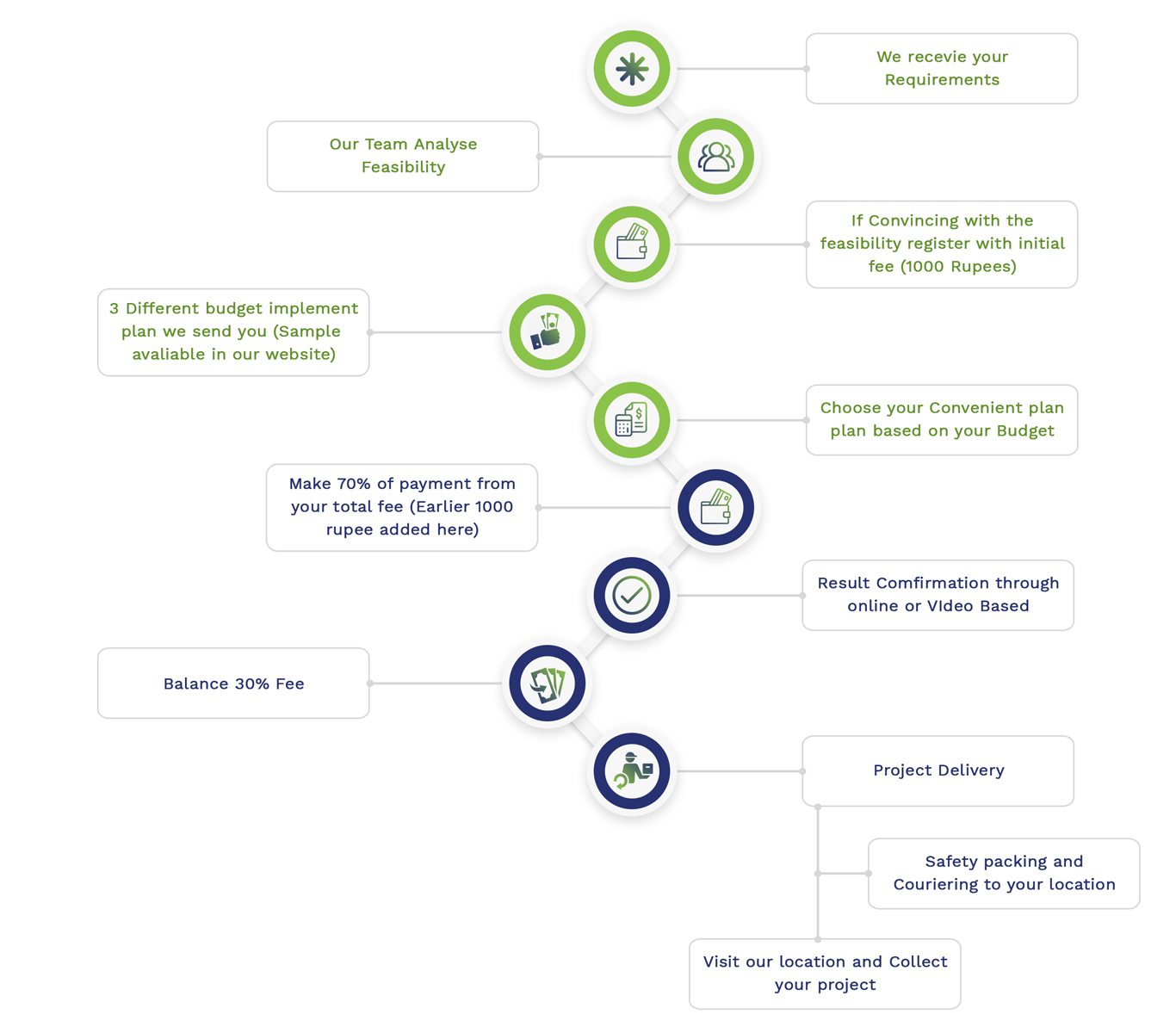
Embedded Projects Workflow

 Matlab
Matlab Simulink
Simulink NS3
NS3 OMNET++
OMNET++ COOJA
COOJA CONTIKI OS
CONTIKI OS NS2
NS2