Measurement Device Independent Quantum Cryptography
In theory, quantum key distribution (QKD) provides information-theoretic security based on the laws of physics. Owing to the imperfections of real-life implementations, however, there is a big gap between the theory and practice of QKD, which has been recently exploited by several quantum hacking activities.
To fill this gap, a novel approach, called measurement-device-independent QKD (mdiQKD), has been proposed. It can remove all side-channels from the measurement unit, arguably the most vulnerable part in QKD systems, thus offering a clear avenue toward secure QKD realisations. Here, we review the latest developments in the framework of mdiQKD, together with its assumptions, strengths, and weaknesses.
Similar IEEE Project Titles:
1Entanglement Sampling and Applications.
2.Quantum Photonic Network: Concept, Basic Tools, and Future Issues.
3.A High-Speed FPGA Implementation of an RSD-Based ECC Processor.
4.Safeguarding Quantum Key Distribution Through Detection Randomization.
5.Risk Analysis of Trojan-Horse Attacks on Practical Quantum Key Distribution Systems.
6.Fast and Generic Inversion Architectures over GF(2m) Using Modified Itoh-Tsujii Algorithms.
7.Time-Bound Anonymous Authentication for Roaming Networks.
8.Implementation of a New Lightweight Encryption Design for Embedded Security.
9.The Error Tolerance Bound for Secure Multi-Qubit QKD Against Incoherent Attack.
10.Scalable Elliptic Curve Cryptosystem FPGA Processor for NIST Prime Curves.
11.Minimizing Pixel Expansion in Visual Cryptographic Scheme for General Access Structures.
12.Customized Certificate Revocation Lists for IEEE 802.11s-Based Smart Grid AMI Networks.
13.User-Defined Privacy Grid System for Continuous Location-Based Services.
14.Effective Key Management in Dynamic Wireless Sensor Networks.
15.Effectively Exploiting Parasitic Arrays for Secret Key Sharing.
16.High-Speed Polynomial Multiplication Architecture for Ring-LWE and SHE Cryptosystems.
17.Adaptively Secure Identity-Based Broadcast Encryption with a Constant-sized Ciphertext.
18.Secret Communication Using Parallel Combinatory Spreading WFRFT.
19.Chaotic Cryptography Using Augmented Lorenz Equations Aided by Quantum Key Distribution.
Subscribe Our Youtube Channel
You can Watch all Subjects Matlab & Simulink latest Innovative Project Results
Our services
We want to support Uncompromise Matlab service for all your Requirements Our Reseachers and Technical team keep update the technology for all subjects ,We assure We Meet out Your Needs.
Our Services
- Matlab Research Paper Help
- Matlab assignment help
- Matlab Project Help
- Matlab Homework Help
- Simulink assignment help
- Simulink Project Help
- Simulink Homework Help
- Matlab Research Paper Help
- NS3 Research Paper Help
- Omnet++ Research Paper Help
Our Benefits
- Customised Matlab Assignments
- Global Assignment Knowledge
- Best Assignment Writers
- Certified Matlab Trainers
- Experienced Matlab Developers
- Over 400k+ Satisfied Students
- Ontime support
- Best Price Guarantee
- Plagiarism Free Work
- Correct Citations
Expert Matlab services just 1-click

Delivery Materials
Unlimited support we offer you
For better understanding purpose we provide following Materials for all Kind of Research & Assignment & Homework service.
 Programs
Programs Designs
Designs Simulations
Simulations Results
Results Graphs
Graphs Result snapshot
Result snapshot Video Tutorial
Video Tutorial Instructions Profile
Instructions Profile  Sofware Install Guide
Sofware Install Guide Execution Guidance
Execution Guidance  Explanations
Explanations Implement Plan
Implement Plan
Matlab Projects
Matlab projects innovators has laid our steps in all dimension related to math works.Our concern support matlab projects for more than 10 years.Many Research scholars are benefited by our matlab projects service.We are trusted institution who supplies matlab projects for many universities and colleges.
Reasons to choose Matlab Projects .org???
Our Service are widely utilized by Research centers.More than 5000+ Projects & Thesis has been provided by us to Students & Research Scholars. All current mathworks software versions are being updated by us.
Our concern has provided the required solution for all the above mention technical problems required by clients with best Customer Support.
- Novel Idea
- Ontime Delivery
- Best Prices
- Unique Work
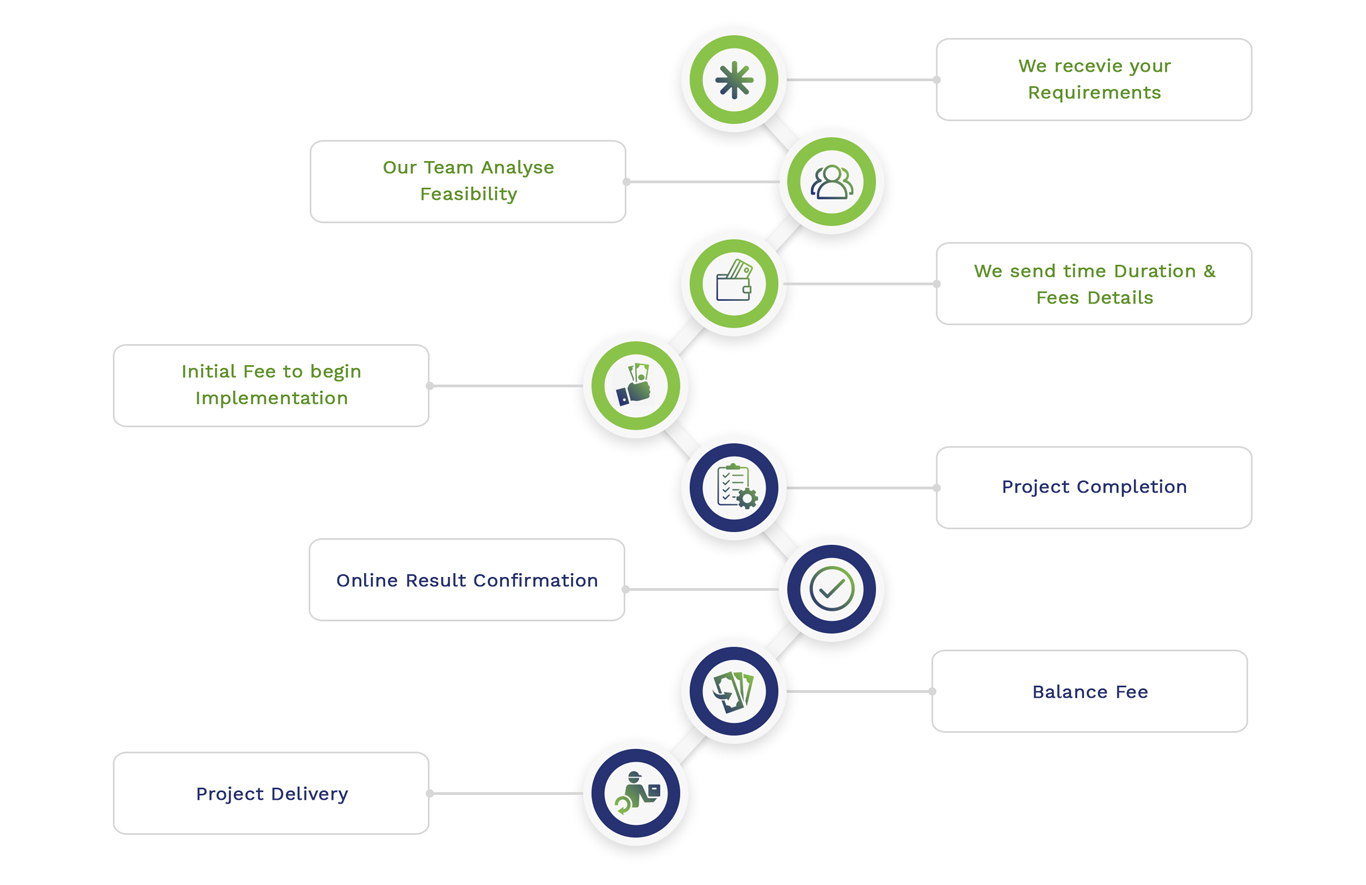
Simulation Projects Workflow
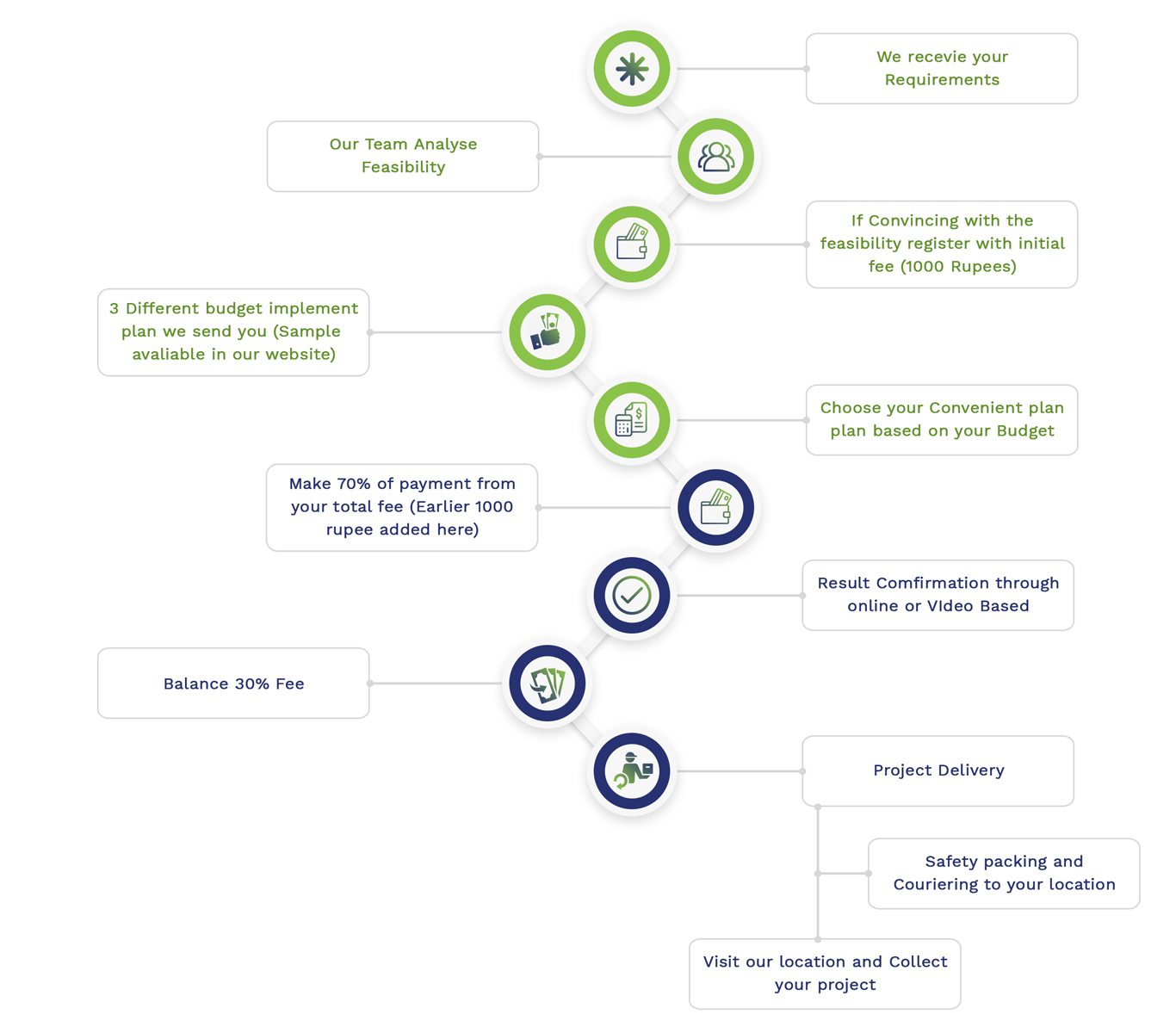
Embedded Projects Workflow

 Matlab
Matlab Simulink
Simulink NS3
NS3 OMNET++
OMNET++ COOJA
COOJA CONTIKI OS
CONTIKI OS NS2
NS2